Having acknowledgement of how differently access control systems are used in different companies and organizations forms a basis for a deeper understanding.
The way access control systems are implemented can vary significantly across organizations because each organization has its own unique needs, goals, and security risks. These differences stem from various factors, including the type of data they handle, the size of the organization, regulatory requirements, and the physical or digital assets they need to protect.
1. Access Control in Healthcare:
Hospitals and healthcare facilities are prime targets for cyberattacks and data breaches due to the sensitivity of patient data. Hospitals need stringent access controls to comply with HIPAA regulations. The impact therefore , would be Better patient confidentiality, streamlined access to critical information, and a reduction in unauthorized access.
2. Access Control in Financial Institutions:
Banks require a robust access control system to ensure the safety of both customer accounts and internal systems. With the rise of cyberattacks targeting financial institutions, access control is vital for protecting sensitive data and transactions.
For example A leading global bank uses a combination of multi-factor authentication (MFA) and geo-location-based access control for employees accessing customer data and internal systems. This kind of step would help prevent fraud.
3. Access Control in Education:
Universities often deal with large populations of students and faculty, requiring an efficient way to manage physical and digital access to buildings, labs, and sensitive research data.
A university implements a smart card access system combined with cloud-based role-based access control to manage access to labs, libraries, and lecture halls. This system also tracks attendance for certain classes or events.
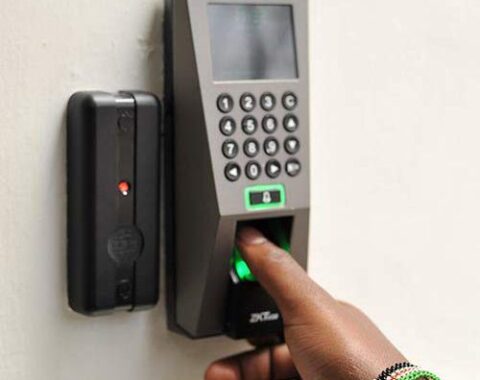
4. Access Control in Manufacturing and Industry:
Manufacturing plants dealing with sensitive product designs or trade secrets require strict access control to protect intellectual property (IP) and prevent industrial espionage.
The impact this will have is Reduced risk of IP theft, better tracking of employee movement, and higher accountability for actions on the production floor.
Access control strategies are tailored to the unique needs, risks, and resources of each organization. What one company prioritizes—whether it’s data protection, physical security, regulatory compliance, or user convenience—will shape how they design their access control systems. Each organization’s threat landscape, user profiles, regulatory requirements, and technology stack all contribute to the way access control is implemented, and understanding these factors can help you explain why access control varies so much from one organization to another. As simplified communications limited we are committed to bring this to reality.